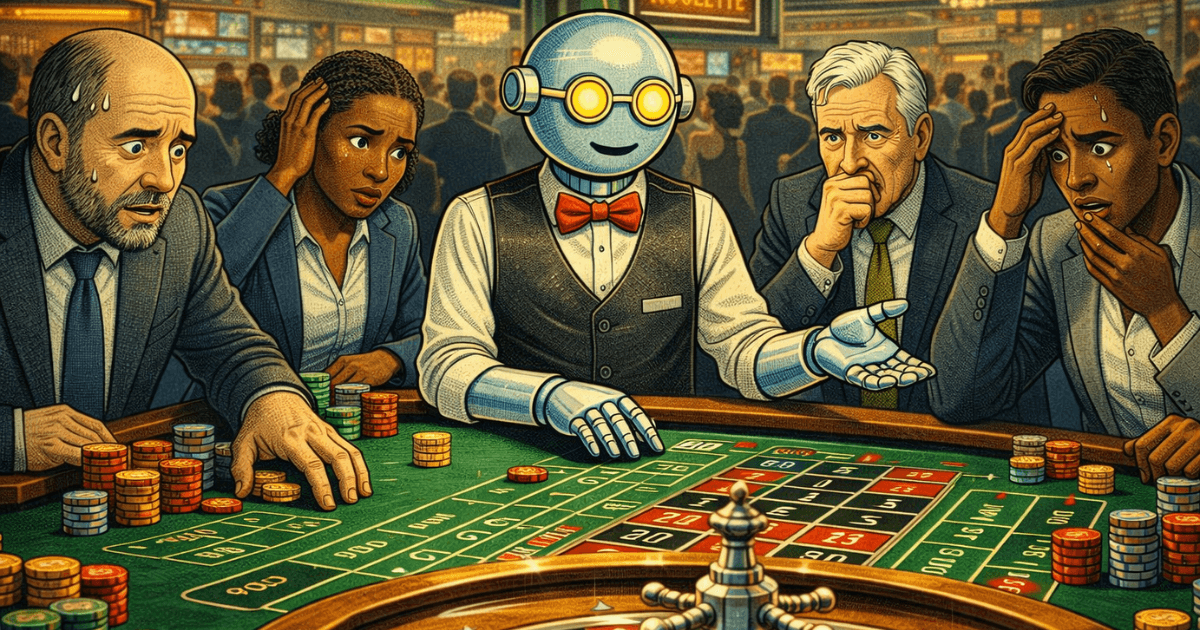
AI Roulette: How CISOs Can Stop Gambling on AI Security
Jason Rebholz
I walked the RSA expo hall this year and came out more confused than when I walked in.
75% of companies claimed to “solve” agentic security. Booths ranged from pizza parlors to old school diners, because you can’t secure agents on an empty stomach. The taglines made bold claims, most of which were indecipherable. After walking the whole floor, I couldn't tell you in plain English what a single one of them actually did to secure agents.
I say all of this as a former CISO and someone who lives, eats, and breathes agentic security. I should have some idea of what these companies are doing, and I came up empty-handed.
It’s no wonder security teams are stressed about securing agents. CISOs today are being handed what feels like an impossible assignment. Enable the business to roll out agents as fast as possible while keeping agents secure so the company doesn't introduce material risk. And you have to figure it out yourself because nobody has a map.
CISOs are sitting at a roulette table with a limited number of chips, trying to bet on what policies, configurations, and products will meet their goal. But unlike a normal roulette wheel with 38 numbers, this one has hundreds, and new ones keep appearing whenever a security vendor refreshes its website every week.
Overnight, API gateways became MCP gateways. SSPMs are now third-party AI security companies. Every CASB has shadow AI covered, too. DLP? Yup, also secures agents. Can’t forget identity. They also secure agents.
Every vendor is staring at the same problem through their own tiny window and old ways of thinking, screaming telling you they can see the whole house.
For the CISO trying to figure out where to place bets, it's not helpful. It's noise.
The Conversation That Keeps Happening
Every week, some version of this conversation shows up in my calendar:
Customer: "Hey, I need a product to secure my agents."
Me: "Okay, tell me more. What part of the problem are you trying to solve?"
Customer: blank stare…
This isn't a knock on anyone. This is what happens when an entire industry finds a new problem space exists before the problem has been properly defined.
The problem is too early, too underdeveloped, and there is no single point solution that solves it all.
Think about how previous cybersecurity challenges evolved. They emerged over decades. With existing security challenges, we have the luxury of knowing the shortcuts. Endpoint security: get EDR. Network security? Firewall, or a WAF, depending on your use case. Application security? SAST, maybe a DAST, done.
Those shortcuts exist because those problems matured over decades. The solutions followed. There's a playbook.
Agent security doesn't have that playbook yet. The problems are still emerging, and every vendor is scrambling to be the ONE to solve it. The solutions are more immature than any vendor wants to admit. And here's the part that makes it genuinely hard: agent security isn't a vertical problem. It's horizontal. It cuts across every single security domain.
There's no single vendor who can cover the whole board. Anyone who tells you differently is selling you something they can’t back up.
The infinite roulette board is paralyzing your decision-making. Every CISO is trying to make intelligent bets with limited chips. The CISO who says "I need to cover everything" is the same CISO who ends up covering nothing well.
The field has to narrow. The question is, how?
Any new journey starts with a first step, but that's cold comfort when you don't know which direction you're facing. What you need before you can plot a course is information. Real information, from your environment, not from a vendor deck or a Gartner quadrant.
Start where every good security journey starts. You can’t make smart bets on a board you can’t see. That’s why security teams should start with visibility.
What does visibility actually look like in practice? It means understanding where AI is being used in your organization, how it's being used, and what it's doing on your behalf. That's it. That's step one.
Once you have that picture, the infinite roulette board suddenly has a lot fewer numbers. The risk areas that matter to you, in your environment, start to surface. And then you can actually work the problem.
Here are four steps that move the needle forward. Once you commit to starting with visibility, the path becomes less terrifying:
1. Deploy and observe. Get eyes into your environment. Telemetry is key here.
2. Assess the usage patterns. Where are agents operating? What actions are they taking? What data are they touching? This data shifts the discussion from theoretical risk to actual risk.
3. Identify your risks. A lot of blogs talk about prompt injection and scary research that makes your knees tremble. The theoretical risks are real, but your environment's actual risks are what matter. Use the data you’ve collected, and compare it to your risk tolerance. Pick the behaviors you see in your environment that shouldn't be happening.
4. Put controls in place. Not everywhere at once. Targeted. Limit the blast radius where the real exposure is.
This isn't a new framework. This is just security. It works for endpoints. It works for cloud. It works for AI agents.
You will go down some rabbit holes. That's fine. The goal is to limit the number of rabbit holes you stumble into blindly and to ensure the ones you go down are worth your team's time and attention.
A well-informed bet against ten things beats a panicked sprint against a million.
The vendors aren't going to stop adding numbers to the board. That's the reality. But the good news is you don't have to play their game.
Start with visibility. Let your environment tell you where the real risk is. Then go solve that problem.
If you’re ready to stop guessing and start with real visibility, Evoke can help.